Complying with the Payment Card Industry Data Security Standard (PCI DSS) is a critical exercise for any organization that stores, processes or transmits card data. Properly understanding the scope of the assessment can head off potentially costly compliance issues, but scoping does not come without challenges.
Understanding Scoping
The scope of PCI DSS as defined by the Payment Care Industry Security Standards Council is as follows:
The PCI DSS security requirements apply to all system components included in or connected to the cardholder data environment. The cardholder data environment (CDE) is comprised of people, processes, and technologies that store, process, or transmit cardholder data or sensitive authentication data. (PCI DSS v3.2, page 10)
This definition quickly invokes gray areas that beg for clarification. Two of the most common areas of debate are 1) which systems need to be included and 2) whether merchants and service providers have different considerations.
Merchants vs. Service Providers
One common misconception is that a PCI assessment is the same for both merchants and service providers. While merchants accept the payment from the cardholder, the service provider processes, stores and/or transmits the cardholder data. They handle and view cardholder data differently, and this must be taken into consideration when scoping the assessment. For instance, there are specific versions of the reporting documents (Report on Compliance or “ROC” and Self Assessment Questionnaire or “SAQ”) just for service providers. Service providers generally have more responsibility for cardholder data security, and therefore have more compliance requirements than merchants.
Which Systems Should be Included
Another common pitfall is incorrectly or incompletely defining the scope of assessment (the systems and processes involved in processing, storing, and/or transmitting cardholder data). Defining scope too narrowly can result in unprotected cardholder data when critical systems are not assessed. Too broad of a definition can result in unnecessary compliance and assessment costs.
Best Practice: Use Scoping Tools
Scoping tools help you avoid costly mistakes by making it clear what systems are in scope of the PCI DSS assessment. There are many tools available to help determine scope, but we will discuss the following three in more detail:
- Diagrams
- Data Discovery Tools
- Open PCI DSS Scoping Toolkit
It is important to note that none of these components are stand-alone solutions for scoping. They are meant to complement each other in order to produce a complete scope picture.
Diagrams
To begin scoping, you must first understand all the systems that are present within the organization. One of the simpler and more effective ways to approach this is to diagram your systems and determine if they are included or connected to the cardholder data environment (see definition from earlier). Common diagrams include use case diagrams, context diagrams, data-flow diagrams and flowcharts.
Example Network Diagram (Source: Cisco)
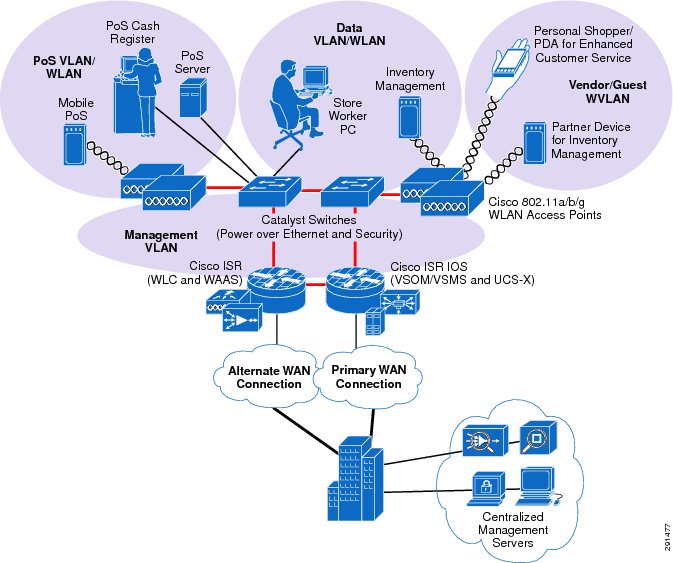
Diagramming helps clarify the relationships between various systems, but the individual performing scoping may not have enough information to complete a comprehensive diagram. Working with team members who are experienced in diagramming data reduces the time required to create the diagram and can result in a more complete diagram. An incomplete diagram can result in systems not being properly categorized as in-scope or out-of-scope, thus taking the time to complete an accurate diagram is a beneficial exercise.
Data Discovery Tools
Data discovery exercises help you develop a comprehensive understanding of how data flows through your organization, and often reveal previously unknown patterns of data handling. Once data discovery has been performed, you will have a more complete picture of where cardholder data resides at rest within your environment. There are numerous data discovery tools available to the public for purchase and also as open source software. The tool that is right for your organization will depend upon the type of environment you want to scan (i.e. Windows, Linux, etc.).
Open PCI DSS Scoping Toolkit
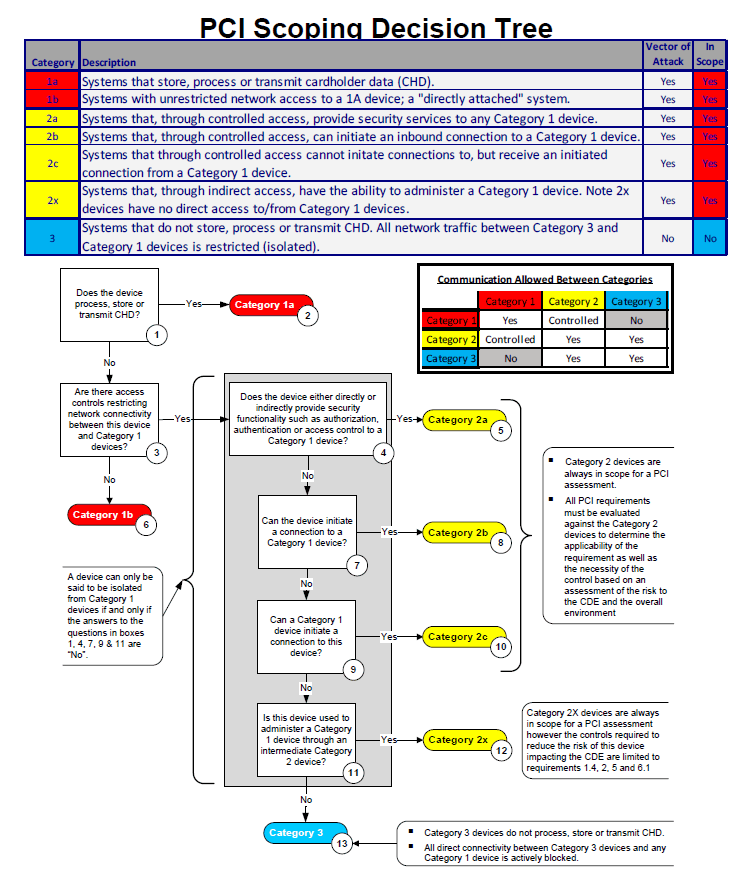
A data discovery exercise can produce an overwhelming amount of data, which may cause more confusion than clarity. It is important to categorize the data with easy to understand definitions, and the Open PCI DSS Scoping Toolkit (“the Toolkit”) is an excellent support for this process. The Open PCI DSS Scoping Toolkit, published by the Open Scoping Framework Group, offers a structured framework and clear definitions of what is in and out of scope, thus identifying key areas of focus in a structured framework.
The Toolkit classifies systems into three categories based on the types of risks associated with the system. If it is not immediately clear whether a particular system is in or out of scope, the Scoping Decision Tree within the Toolkit offers a walkthrough. By the end of the decision tree process, all systems can be clearly categorized into one of the three categories, and you will have defined your PCI scope.
Excerpt from the Open PCI DSS Scoping Toolkit Scoping Decision Tree (Page 18)
Takeaway
Diagrams, data discovery tools and the Open PCI DSS Scoping Toolkit assist organizations in properly scoping an assessment. However, none should be considered the sole tool in the scoping “toolbox”. It is important to understand how the cardholder data is being handled by all systems. Seeking the right expertise at the outset of the scoping exercise can increase efficiency and accuracy of the scoping exercise.
If you have questions about scoping your cardholder data environment, contact a PCI expert at Frazier & Deeter: https://frazierdeeter.staging.wpengine.com/services/advisory/pci-payment-card-industry/
About the Authors
 Mindy Regen, CISA,QSA, CCSFP, PCIP
Mindy Regen, CISA,QSA, CCSFP, PCIP
As a Director, Mindy contributes 15 years of internal and IT audit experience to the Process, Risk & Governance practice of Frazier & Deeter. With her extensive PCI, SOX, internal audit and security audit experience, Mindy manages and contributes to the delivery of internal control and IT and security advisory assessments across a wide range of industries with a focus on financial services, restaurants, hospitality, manufacturing, distribution, healthcare and traditional and eCommerce retail.
